The Cisco SD-WAN vSmart installation and configuration process is exactly the same as for vBond controller. Install vSmart, install certificate for vSmart, and finally create DTLS tunnels between vSmart with vBond and vManage controllers. DTLS Tunnels will be used to transfer management and control traffics between controllers.
what is vSmart?
vSmart is control-plane section of SD-WAN infrastructure. The main task of vSmart is to announce routing information between WAN routers, via OMP protocol (Overlay Management Protocol). This protocol is similar to BGP, but it is used in SD-WAN infrastructure. vSmart also handles key and policy exchange used for IPSec tunnels between WAN routers. All of these control traffic are negotiated securely via DTLS tunnel between the vSmart and the WAN routers. Data traffic itself between the WAN routers are transmitted via IPSec tunnel.
4. cisco SD-WAN vManage Installation and Configurationn (Version 20.3.4)
Cisco SD-WAN powered by Viptela
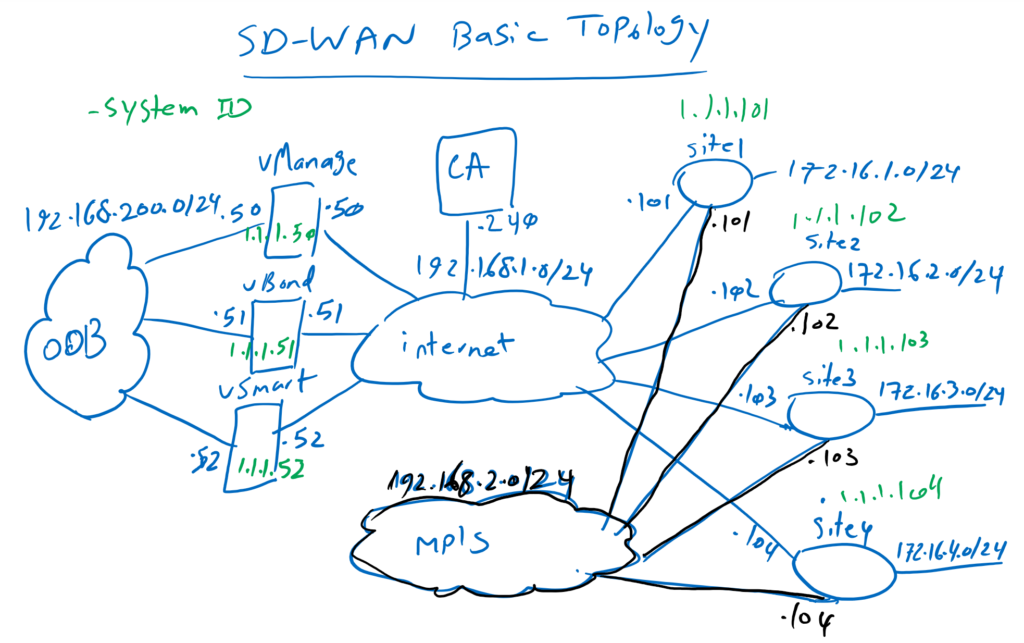
Just to review, vSmart is connected to both Out of Band Management (OOB) network and Internet transport. IP address 192.168.200.52 is the address of OOB and 192.168.1.52 is the address of the interface connected to the Internet transport. 1.1.1.52 is the IP address that we will configure as system-ip in vSmart controller.
vSmat Installation
We start by importing vSmart OVF like what we did for vManage and vBond controllers.
We need two network adapters, the first adapter for OOB and the second adapter to be connected to internet transport. By default, vSmart has one network adapter. So I add another network adapter.
After adding the second adapter, now I can power on the machine.
Now let’s review the configuration and then configure vSmart controller.
As you can see the first adapter (eth0) is used as OOB and the second transport eth1 is used to connect to the internet. 192.168.200.52 will be configured in eth0 and 192.168.1.52 will be configured in eth1.
!!!!! vSmart
!
Adpater1 (VM Network 1) for oob : eth0
Adpater2 (VM Network 1) for transport: eth1
!
user: admin
pass: admin --> rayka-co.ir
By default, username and passwords are admin/admin. The password is changed to rayka-co.com like what we did in vManage and vBond Controller.
The system configuration is the same as vManage and vBond. Hostname, system-ip, site-id, Organization name , vBond IP address and NTP will be configured in vSmart controller. The details of each of these commands are already explained in vManage installation process.
!!!!! vSmart
system
host-name vSmart
system-ip 1.1.1.52
site-id 100
domain-id 1
organization-name RAYKA
vbond 192.168.1.51
clock timezone Aisa/Tehran
ntp server 37.156.28.13 prefer vpn 0
show configuration
commit
!
vpn 0
ip route 0.0.0.0/0 192.168.1.1
no interface eth0
interface eth1
ip address 192.168.1.52/24
no shutdown
commit
vpn 512
interface eth0
ip address 192.168.200.52/24
no shutdown
commitThen we configure VPN 0 and VPN 512.VPN 512 is used as the management VRF and VPN 0 as default VRF. interface eth0 is configured in VPN 512 with IP address 192.168.200.52. interface eth1 is configured inside VPN 0 with IP address 192.168.1.52. default route is configured in VPN 0 with gateway address 192.168.1.1. Default route can also be configured in VPN 512 but I have not configured, since my management client is directly connected to OOB network.
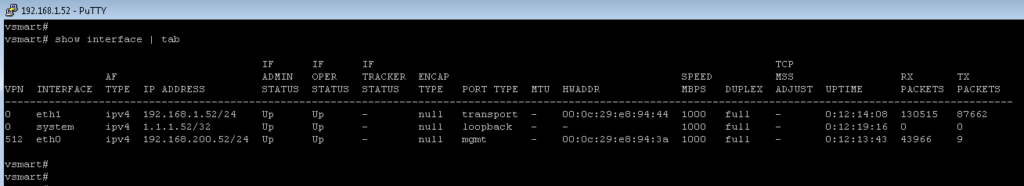
vsmart# show interface | tab
IF IF IF TCP
AF ADMIN OPER TRACKER ENCAP SPEED MSS RX TX
VPN INTERFACE TYPE IP ADDRESS STATUS STATUS STATUS TYPE PORT TYPE MTU HWADDR MBPS DUPLEX ADJUST UPTIME PACKETS PACKETS
-----------------------------------------------------------------------------------------------------------------------------------------------------------------
0 eth1 ipv4 192.168.1.52/24 Up Up - null transport - 00:0c:29:e8:94:44 1000 full - 0:12:14:08 130515 87662
0 system ipv4 1.1.1.52/32 Up Up - null loopback - - 1000 full - 0:12:19:16 0 0
512 eth0 ipv4 192.168.200.52/24 Up Up - null mgmt - 00:0c:29:e8:94:3a 1000 full - 0:12:13:43 43966 9
vsmart# ping 8.8.8.8
Ping in VPN 0
PING 8.8.8.8 (8.8.8.8) 56(84) bytes of data.
64 bytes from 8.8.8.8: icmp_seq=1 ttl=107 time=59.6 ms
64 bytes from 8.8.8.8: icmp_seq=2 ttl=107 time=58.7 ms
64 bytes from 8.8.8.8: icmp_seq=3 ttl=107 time=54.3 ms
^C
--- 8.8.8.8 ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2001ms
rtt min/avg/max/mdev = 54.312/57.586/59.668/2.343 ms
vSmart Certificate Installation
Now we will install certificate and then create DTLS Tunnel from vSmart with other controllers.
First we have to add vSmart controller in vManage.
Configuration -> devices -> controllers -> add controller -> vSmart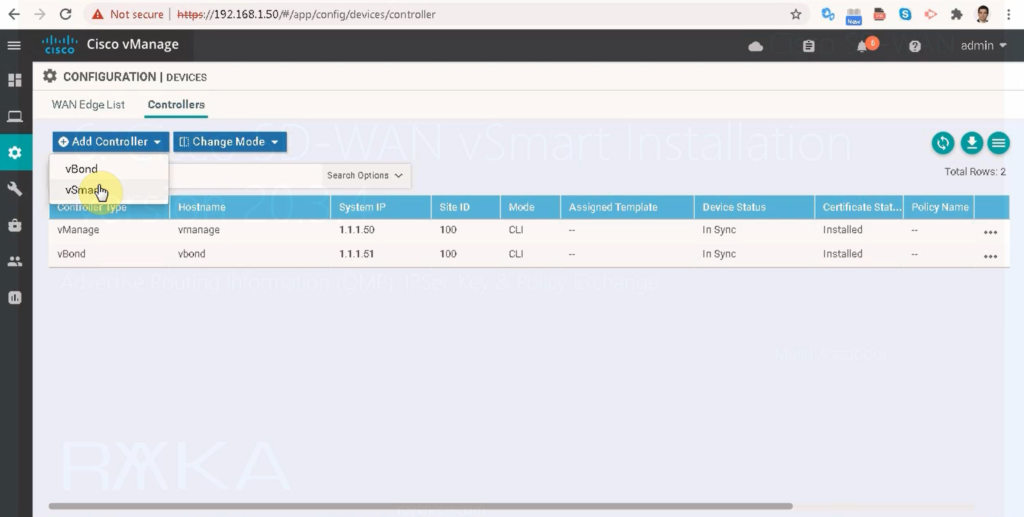
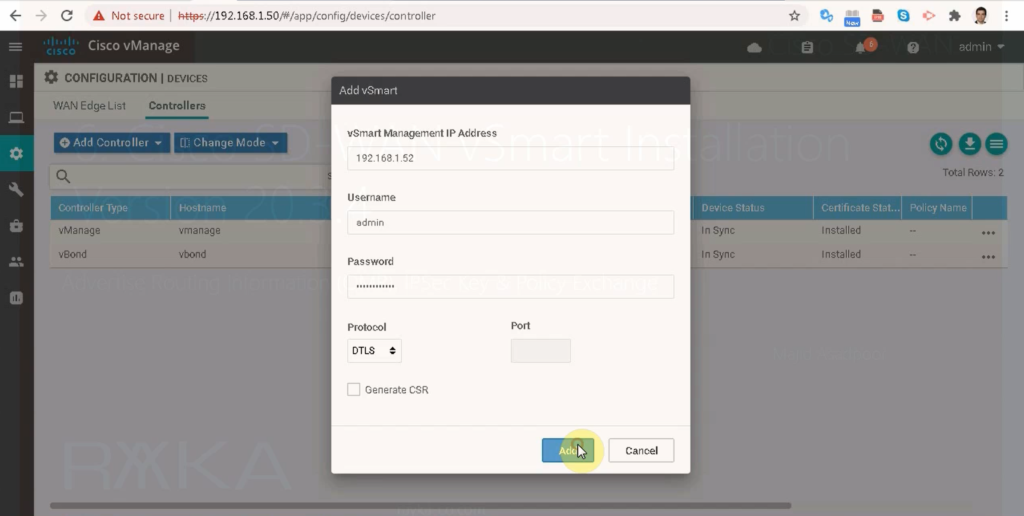
We give IP address, username and password of vSmart. CSR will be created in a few minutes.so we ignore it in this step.
When vSmart is added in vManage, CA certificate is automatically copied into vSmart controller. we can check it with the following command.
vsmart# show certificate root-ca-cert | inc rayka
Issuer: DC=local, DC=rayka-co, CN=CA
Subject: DC=local, DC=rayka-co, CN=CA
Now we can request and install certificate for vSamrt.
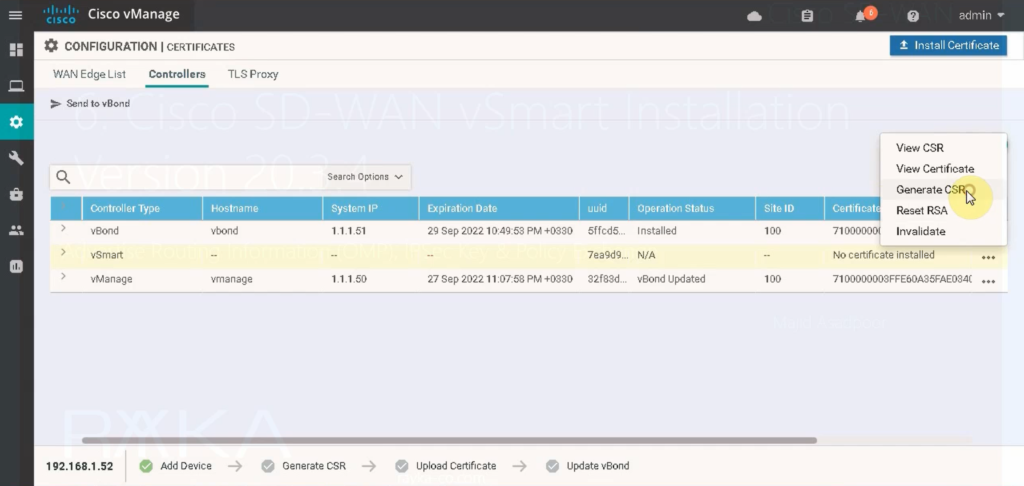
Configuration -> certificate -> controllers -> vSamrt -> generate CSR -> copy csr
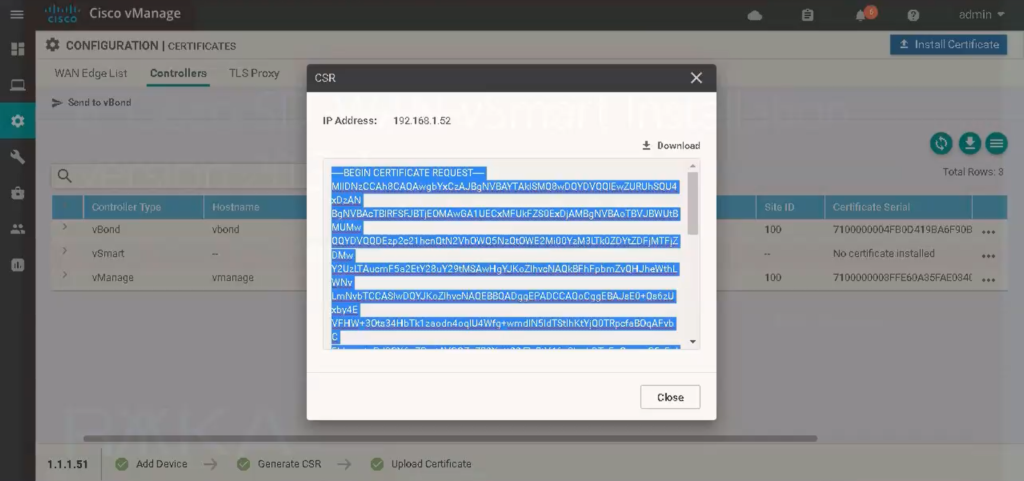
http://192.168.1.240/certsrv -> request a certificate -> advanced certificate request -> paste csr -> use sdwan template -> save with vSamrt name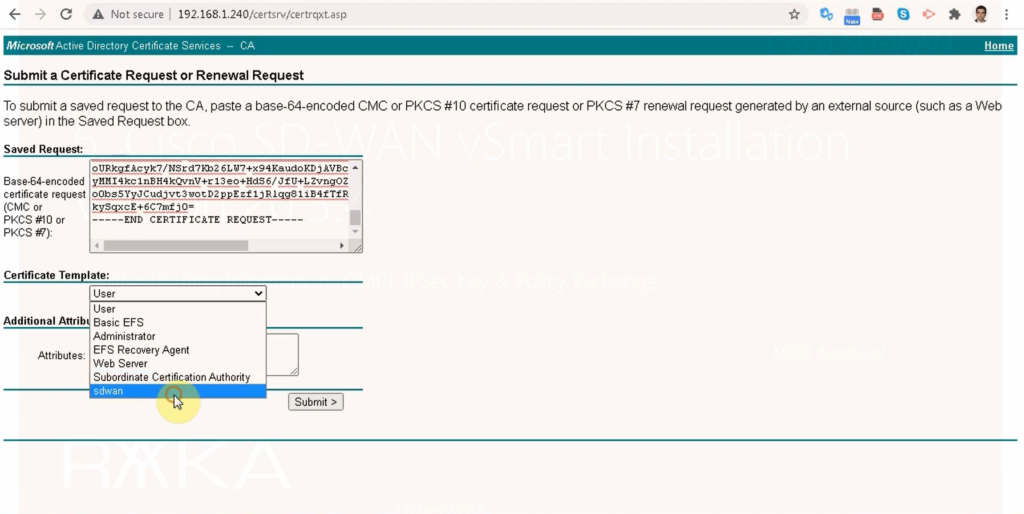
received certificate, now can be installed in vManage interface.
Configuration -> certificate -> controllers -> vSamrt -> Install Certificate -> add generated vBond certificate.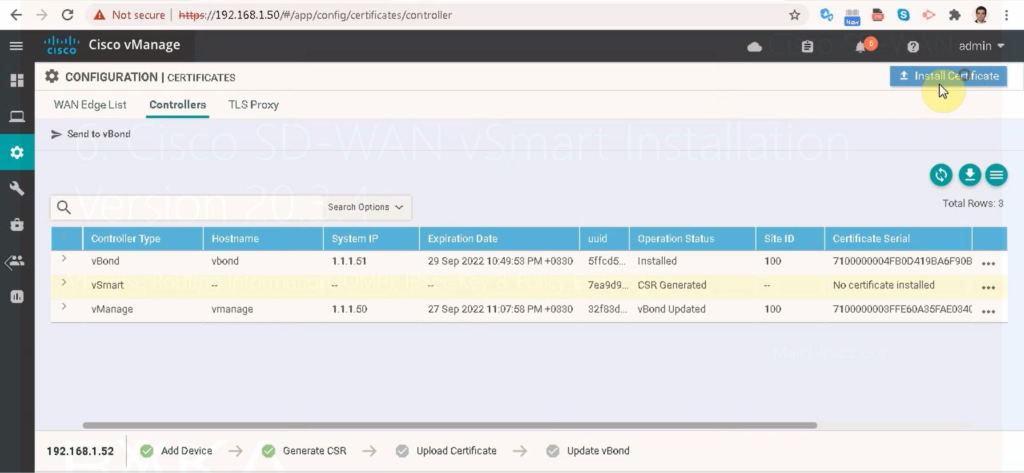
You can see that the certificate is installed but not yet in sync. We need to create DTLS tunnels between vManage and vBond so that they can be synchronized.
Configuration -> devices -> controllers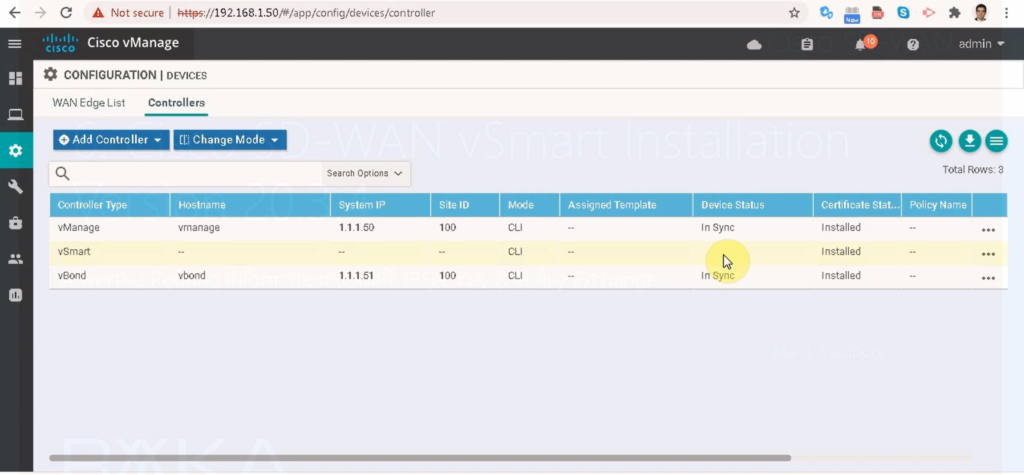
Create vSmart DTLS Tunnels
DTLS Tunnel is already created in vManage and vBond. Now it must be created in vSamrt controller. Tunnel is created over internet transport. eth1 is in default VRF and connected to internet transport.
We create tunnel interface and allow all services in Tunnel interface.
!!! vSmart
vpn 0
int eth1
tunnel-interface
allow-service all
commitNow we have to check in vSmart to make sure if DTLS tunnels with vBond and vManage come up.
Two DTLS Tunnels must be created with vBond and one DTLS tunnel with vManage.
vsmart# show control connections
PEER PEER
PEER PEER PEER SITE DOMAIN PEER PRIV PEER PUB
INDEX TYPE PROT SYSTEM IP ID ID PRIVATE IP PORT PUBLIC IP PORT REMOTE COLOR STATE UPTIME
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
0 vbond dtls 0.0.0.0 0 0 192.168.1.51 12346 192.168.1.51 12346 default up 0:12:42:18
0 vmanage dtls 1.1.1.50 100 0 192.168.1.50 12346 192.168.1.50 12346 default up 0:12:42:12
1 vbond dtls 0.0.0.0 0 0 192.168.1.51 12346 192.168.1.51 12346 default up 0:12:42:18
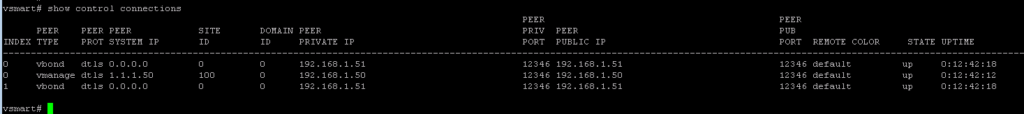
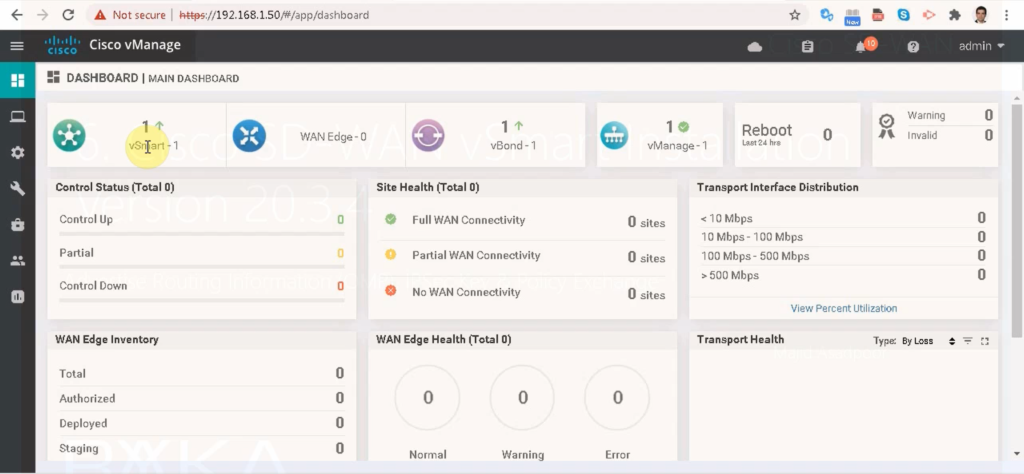
Now you can also check in the vManage dashboard if vSmart has been added to the list. if The color is green, it means it is activated and ok.
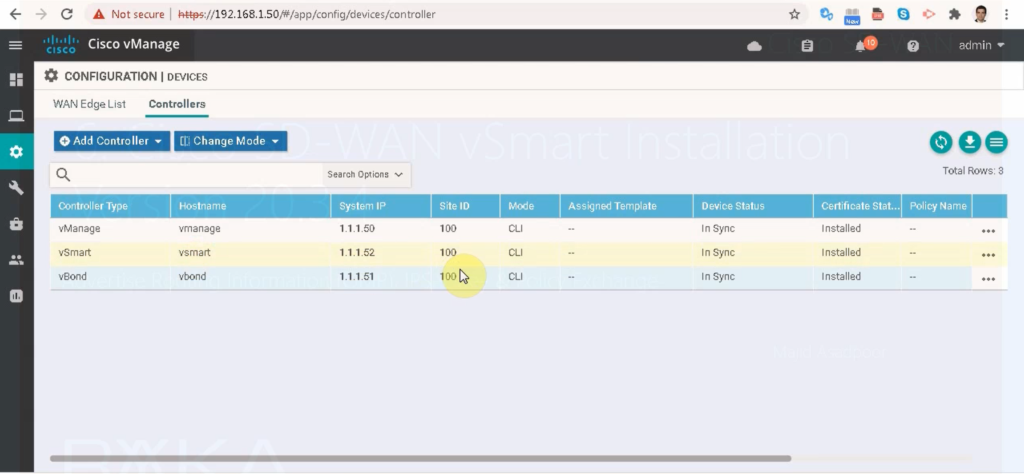
In Configuration -> Devices -> Controllers, you should see that it is now in sync and the third controller is added to SDWAN infrastructure.
New to this subect.can I have access to ful training please
Hi
complete course will be published gradually